Learn more about Smart Home Security
Article Outline
– Why smart home security matters now: context, trends, and common risks
– Core components: sensors, cameras, locks, lighting, sirens, and hubs
– Connectivity and reliability: Wi‑Fi, Zigbee, Z‑Wave, Thread, and Matter
– Privacy and data protection: encryption, storage, and access control
– Designing a layered defense: placement, automations, and maintenance
– Costs, ROI, and a 90‑day roadmap: plan, iterate, and sustain
This outline sets the path from foundational concepts to practical execution. It starts with the “why,” builds through the “how,” and lands on “what next,” so you can move from browsing devices to building a coherent, resilient setup that suits your home, habits, and budget.
Why Smart Home Security Matters Now
Security is not a single gadget; it is a system shaped by your layout, routine, and risk tolerance. Smart home security brings sensors, software, and automation together so your home can notice and react to events in minutes rather than hours. The relevance has grown as households adopt connected devices, remote work increases time at home, and deliveries normalize frequent door activity. At the same time, opportunistic crime remains largely about quick access through doors and windows. A visible, well‑tuned system can deter casual attempts, surface anomalies, and help you respond decisively.
Consider how modern threats mix convenience with oversight gaps. Unlocked side gates, a spare key under a mat, or a dark porch all invite testing. Smart security reduces these openings by making it harder to approach unnoticed and easier to verify what is happening. Practical wins include: timely mobile alerts, event‑triggered lighting, and recorded clips that show context. Studies in environmental design have long noted that lighting, signs, and perceived surveillance reduce attempts; adding connected sensors extends that deterrence with real‑time evidence and automation.
Why it matters today comes down to three factors. First, responsiveness: seconds count when deciding to call a neighbor, sound a siren, or contact authorities. Second, coverage: you can monitor multiple entry points and common pathways without being physically present. Third, adaptability: scenes and schedules adjust as your life shifts, from a new pet to a remodel. While no setup guarantees outcomes, layered measures stack the odds in your favor. With a clear plan, the technology supports your routines instead of complicating them.
Before buying devices, define goals in plain terms: deter, detect, document, and respond. That framing will guide choices on placement, notification rules, and storage. The rest of this guide turns those goals into concrete decisions you can implement at your own pace.
Core Components and How They Work Together
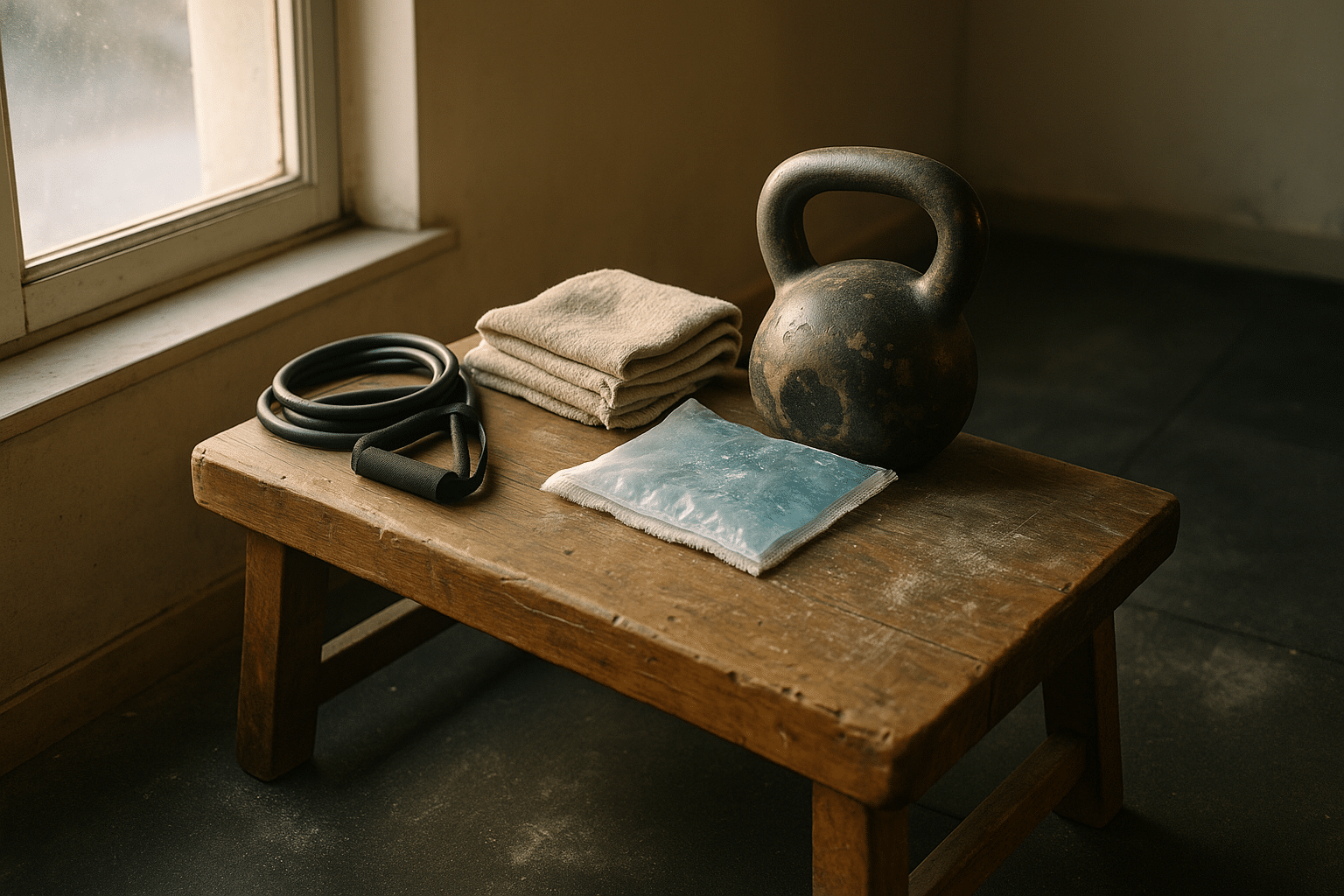
A reliable smart security system starts with simple building blocks that perform specific jobs well. Door and window contact sensors confirm the exact moment a seal breaks. Motion sensors watch interior zones and hallways, catching movement that bypasses perimeter points. Cameras document and deter, offering visual proof and context. Smart locks manage access without spare keys. Sirens and smart lighting provide immediate, attention‑grabbing responses. A hub or controller stitches these pieces into a coherent system, while your network carries the signals.
The value emerges from coordination rather than raw gadget count. For example, a contact sensor at a back door paired with a motion sensor in the adjacent mudroom reduces false alarms while increasing certainty. If the door opens during an “away” scene, the system can turn on lights, trigger a short siren chirp, and start recording on nearby cameras. That same gear behaves differently when you are home: a gentle chime and a push alert might be more appropriate. Scenes (home, away, night, vacation) convert “if this, then that” logic into daily routine.
Comparisons help when choosing components:
– Contact sensors: smaller, discrete units are easier to place on narrow frames; look for long battery life and tamper detection.
– Motion sensors: models with adjustable sensitivity and pet immunity reduce nuisance alerts; ceiling mounts see wider spaces but require testing for blind spots.
– Cameras: resolution and night performance matter, but placement and lighting matter more; a stable mount and modest downward angle reduce glare and sky washout.
– Smart locks: consider mechanical security first (solid bolt, reinforced strike plate), then add features like auto‑lock and temporary codes.
– Sirens: indoor sirens boost urgency; pairing with exterior lighting increases neighborhood awareness without excess noise.
Local logging on a hub adds resilience when the internet drops, while selective cloud storage provides off‑site backup. Redundancy is wise: two sensors on a critical entry, or overlapping camera views at front and side approaches. Treat the system like a team: each role is clear, but overlaps catch what single devices may miss. Start small, verify performance for two weeks, then expand. This approach prevents feature sprawl and keeps maintenance manageable.
Connectivity and Reliability: Wi‑Fi, Zigbee, Z‑Wave, Thread, and Matter
Reliable communication is the quiet backbone of smart security. Many homes mix radios to balance range, battery life, and interference. Wi‑Fi offers bandwidth for cameras and hubs, while low‑power meshes such as Zigbee, Z‑Wave, and Thread excel at sensors and switches. Understanding these layers helps you avoid dead zones and flakey alerts.
Wi‑Fi is familiar and fast, but it shares spectrum with microwaves, cordless phones, and neighbors. Two points matter most: signal strength and congestion. 2.4 GHz generally reaches farther and penetrates walls better than 5 GHz, which is faster but shorter‑range. For static devices like cameras, prioritize steady signal over peak speed. A modest bitrate with consistent connectivity outperforms a high bitrate that drops frames. Channel planning also helps: separate cameras onto less crowded channels and reserve strong SSIDs for security gear. Where feasible, wire cameras with Ethernet to remove a major variable.
Zigbee and Z‑Wave form meshes where powered devices relay messages for battery‑powered sensors. This design reduces power draw and extends reach into corners and attics. Placement of repeaters (for example, smart plugs or in‑wall switches) matters more than raw radio specs; one well‑placed repeater near a metal‑framed doorway can stabilize a whole cluster of sensors. Thread is a newer mesh oriented around IP, enabling low‑power devices to speak the same language as the broader internet. It aims to simplify setup and improve reliability across vendors.
Matter, a device interoperability standard, focuses on letting products join the same home network and coordinate securely, regardless of brand. For security use, that means simpler pairing, consistent control, and less risk of being locked into a single ecosystem. In practice, hybrid systems remain common. A typical layout might be: Wi‑Fi for cameras and hub, Zigbee or Thread for sensors, and Matter to unify control apps. Tips to strengthen reliability include:
– Add mesh repeaters near difficult zones like garages and basements.
– Keep hubs centrally located and elevated to reduce obstructions.
– Use battery status alerts and replace cells proactively, not reactively.
– Test failover behavior by intentionally disconnecting internet for ten minutes and observing system responses.
Reliability is not about perfection; it is about predictable behavior under stress. Plan for the occasional packet loss with short alert delays, duplicate triggers, and local automations that do not depend on remote servers.
Privacy and Data Protection: Encryption, Storage, and Responsible Settings
Security that ignores privacy is incomplete. Your system handles sensitive data: who comes and goes, when rooms are occupied, and what valuables are visible. Treat these insights like keys. Start by choosing devices and hubs that use strong, documented encryption for data in transit (for example, transport‑level encryption) and at rest (for example, device‑level encryption on storage). Local processing reduces exposure: motion analysis on the camera or hub means fewer raw video streams traveling across networks.
Decide where footage lives. Cloud storage is convenient for off‑site backup and remote sharing, but it depends on subscription tiers and vendor retention policies. Local storage on a hub or network drive grants control and can be faster to review. A blended model is practical: keep routine clips locally and upload only high‑priority events. To reduce risk surface:
– Use unique, strong passwords and enable multi‑factor authentication everywhere.
– Limit admin accounts; grant guests or family read‑only access where feasible.
– Disable unnecessary features by default, such as broad location sharing or microphone access in rarely used rooms.
Privacy also involves camera ethics and placement. Aim cameras at your property lines and entry points, not at neighbors’ windows or shared walkways. Indoors, favor common areas like entries and hallways rather than private spaces. Add privacy shutters or schedules that disable indoor cameras when you are home, relying on door contacts and perimeter coverage instead.
Keep software current. Firmware updates often include security fixes that address newly discovered vulnerabilities. Schedule a monthly check for updates, review access logs for unusual sign‑ins, and confirm that old devices are removed from your account. If you sell or donate gear, factory‑reset it and wipe storage where possible.
Finally, document your choices. Note which devices store data locally, which use cloud services, who has access, and how long clips are retained. A one‑page policy for your own household reduces confusion later and makes audits simple. By treating privacy as a first‑class requirement, you gain the confidence to use more automation without compromising your personal boundaries.
Designing a Layered Defense: Placement, Automation, and Maintenance
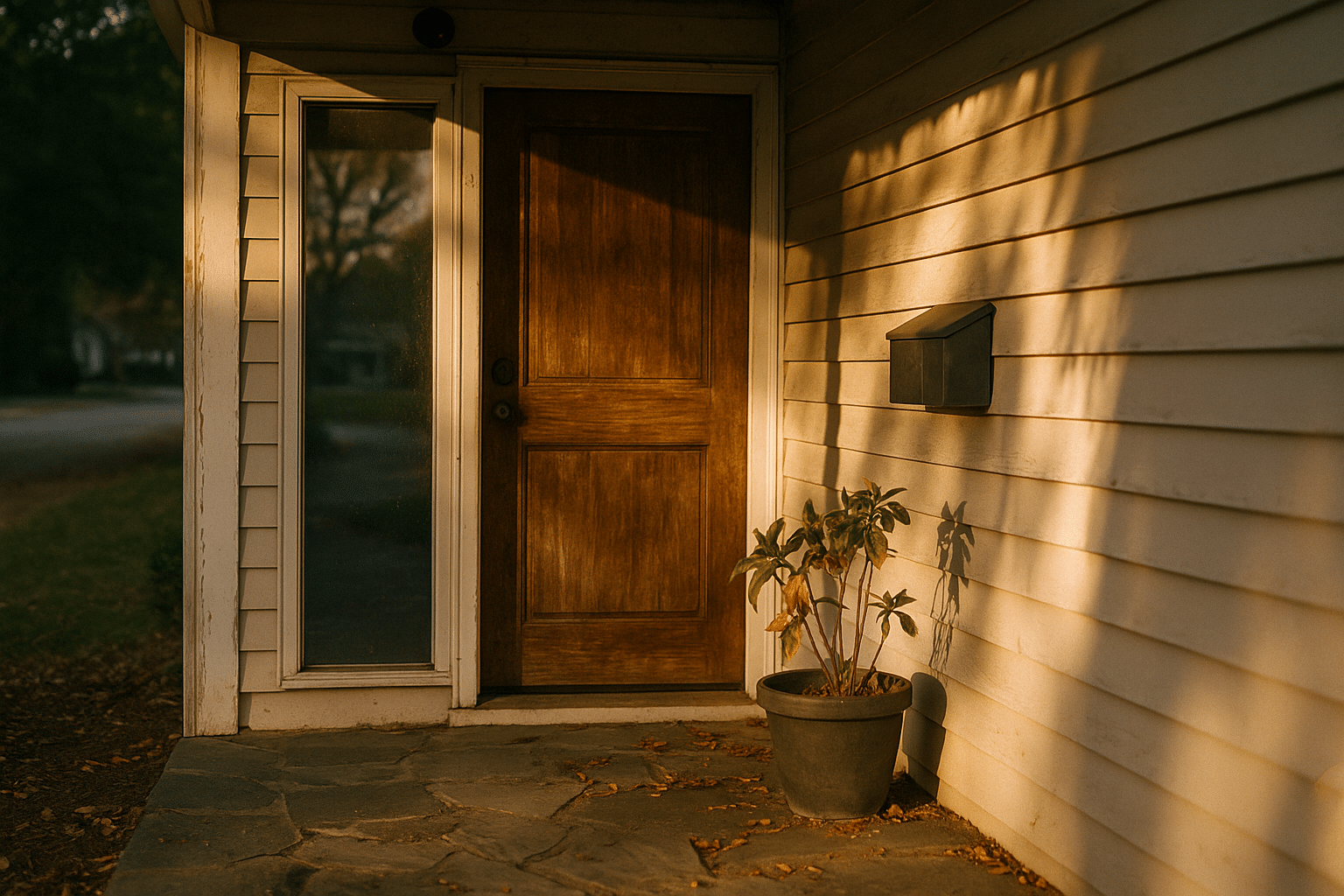
Effective security is layered: outer perimeter, entry points, and interior movement. Start outside by making approaches visible and predictable. Motion‑activated lighting that brightens walkways and porches reduces shadows and uncertainty. A sign indicating active monitoring contributes deterrence without confrontation. Pair this with a camera that frames the approach rather than the street, and a contact sensor on gates or side doors that often receive less attention.
At entry points, focus on clarity and speed. A contact sensor on each exterior door is foundational. Reinforce the door hardware with a solid strike plate and long screws; physical strength complements digital alerts. Place a camera at chest height angled slightly down to capture faces or identifying features without glare from the sky. Avoid mounting too high; a steep angle mostly records hats and hoods. Inside, position a motion sensor to watch the path from the entry to a main room. This overlap improves event confidence: two triggers within a short window raise priority without flooding your phone.
Automations translate detection into action:
– Night mode: if a door opens after bedtime, turn on hallway lights to 30% and send a high‑priority alert.
– Away mode: if both door contact and interior motion trigger within 30 seconds, sound a siren and start recording on all nearby cameras.
– Delivery window: during typical delivery hours, send a snapshot instead of a loud alert to reduce fatigue.
– Vacation mode: simulate occupancy with staggered lighting scenes that vary by day to avoid predictable patterns.
Maintenance keeps reliability high. Test weekly: open a door, walk through a motion zone, and confirm alerts arrive. Replace or recharge batteries on a schedule rather than waiting for low‑power warnings. Dust camera lenses and sensor covers; small smudges can cause soft focus and false motion from glare. Review automations quarterly and adjust for seasonal changes in daylight and activity. Document your device list, last battery change, and any odd behavior in a simple checklist.
Finally, prepare for outages. A hub with battery backup can keep automations running during brief power cuts. Consider a cellular or backup communication path for critical alerts if internet service is unreliable in your area. Redundancy does not need to be elaborate; even overlapping sensor coverage and a neighbor contact plan raise resilience. Layer by layer, you build a system that notices, responds, and recovers.
Costs, ROI, and a 90‑Day Roadmap (Conclusion)
Budgeting for smart security is easier when you separate one‑time gear from ongoing services. Expect a starter kit of contacts, a motion sensor, a hub, and one or two cameras to require a modest, one‑time outlay. Adding smart locks, exterior cameras, and lighting increases upfront costs but also deepens deterrence and convenience. Ongoing expenses may include optional cloud storage, cellular backup, or professional monitoring. Local storage and self‑monitoring reduce subscriptions, though they shift more responsibility to you.
Return on investment includes avoided incidents, faster resolution, and daily quality‑of‑life gains. Clear video and timestamped sensor logs simplify conversations with neighbors or authorities after a package dispute or a minor incident. Some insurers offer small discounts for monitored systems or documented protective devices; confirm details before planning around them. Less quantifiable, but meaningful, is the sense of control that comes from verified alerts and friction‑free access for family, guests, or service providers.
Use this 90‑day roadmap to move from planning to a stable, low‑maintenance setup:
– Days 1‑7: Define goals (deter, detect, document, respond). Map entries, common paths, and dark zones. Choose a hub and two or three high‑impact devices. Create scenes (home, away, night).
– Days 8‑21: Install contact sensors on main doors, a motion sensor in a central hallway, and one camera at the primary approach. Test daily. Tune notification levels to avoid fatigue.
– Days 22‑45: Add lighting automations and a second camera or sensor to cover a blind spot. Document settings. Enable multi‑factor authentication and set up local storage or measured cloud retention.
– Days 46‑75: Expand coverage to secondary entries. Place a repeater to strengthen the mesh where signals are weak. Practice an “internet down” drill and verify local automations work.
– Days 76‑90: Review video angles, battery status, and event logs. Simplify any noisy rules. Decide whether optional services (monitoring or cellular backup) match your risk profile.
Conclusion for homeowners: Smart home security pays off when it is tailored, layered, and tested. Favor simple, robust components over novelty, and let automation support your habits instead of dictating them. Keep privacy front and center, maintain your gear, and revisit settings as life changes. With a clear plan and steady iteration, you gain a calmer home that quietly watches your back without getting in your way.